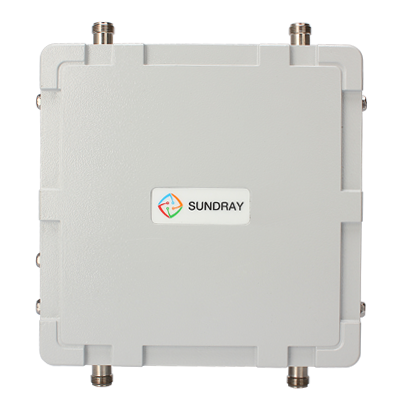
Sundray AP-S800 Outdoor Wireless Access Point
SUNDRAY AP-S800 is an outdoor high-speed wireless access point that supports 802.1a/b/g/n dual-frequency access launched by SUNDRAY. AP-S800 adopts the 2x2 MIMO technology and supports dual frequencies of 802.11a/n and 802.11b/g/n to provide a high transmission rate up to 600 Mbps. AP-S800 uses a Gigabit port for uplink to ensure high-speed wireless transmission and PoE for remote power supply to simplify network deployment.
SUNDRAY AP-S800 is an outdoor high-speed wireless access point that supports 802.1a/b/g/n dual-frequency access launched by SUNDRAY. AP-S800 adopts the 2x2 MIMO technology and supports dual frequencies of 802.11a/n and 802.11b/g/n to provide a high transmission rate up to 600 Mbps. AP-S800 uses a Gigabit port for uplink to ensure high-speed wireless transmission and PoE for remote power supply to simplify network deployment.
SUNDRAY AP-S800 is an outdoor high-speed wireless access point that supports 802.1a/b/g/n dual-frequency access launched by SUNDRAY. AP-S800 adopts the 2x2 MIMO technology and supports dual frequencies of 802.11a/n and 802.11b/g/n to provide a high transmission rate up to 600 Mbps. AP-S800 uses a Gigabit port for uplink to ensure high-speed wireless transmission and PoE for remote power supply to simplify network deployment.
The shell of AP-S800 is of the IP 68 protection level and boasts waterproof, damp proof, dustproof, fireproof, and sun protection features. The shell can protect AP-S800 against severe weather and environments. This ensures that AP-S800 is applicable to both damp and cold areas. AP-S800 also supports the point-to-point and point-to-multipoint relay bridge function, improving the feasibility of outdoor networking. AP-S800 works with SUNDRAY NAC series controllers to provide unprecedented quick access experience and secure service access for users.
AP-S800 provides four N-type external antenna interfaces. Omnidirectional antenna or directional antenna can be selected based on the actual environment. It applies to outdoor environments such as scenic spots, schools and parks, squares, etc.
|
Item |
Description |
|
|
Model |
S800 |
|
|
Dimensions (excluding antenna interfaces and accessories) |
210 mm x 210 mm x 70 mm |
|
|
Ethernet port |
A 10/100/1000M Ethernet port |
|
|
Console port |
1 RJ45 port |
|
|
PoE |
48 V, 800 mA |
|
|
Transmit power |
≤ 27 dBm |
|
|
Power adjustment granularity |
1 dbm |
|
|
Power range |
3 dBm to the value specified by national regulations |
|
|
Power consumption |
< 35 W |
|
|
Antenna |
External antenna |
|
|
Antenna interface |
Two 2.4 GHz N-type connectors and two 5 GHz N-type connectors |
|
|
Reset/restore factory settings |
None |
|
|
Status indicator |
None |
|
|
Operating/storage temperature |
-40ºC to +65ºC |
|
|
Operating/storage humidity |
0%-100% (non-condensing) |
|
|
Protection level |
IP 68 |
|
|
MTBF |
> 250000 H |
|
|
Item |
Description |
|
|
Model |
S800 |
|
|
RF |
Streams |
2 |
|
Maximum transmission speed of a single frequency |
300 Mbps |
|
|
Operating frequency band |
802.11b/g/n: 2.4-2.483 GHz (China) |
|
|
802.11a/n: 5.725-5.850 GHz (China) |
||
|
Modulation technology |
OFDM: BPSK@6/9 Mbps, QPSK@12/18 Mbps, 16-QAM@24 Mbps, 64-QAM@48/54 Mbps |
|
|
DSSS: DBPSK@1 Mbps, DQPSK@2 Mbps, [email protected]/11 Mbps |
||
|
MIMO-OFDM: MCS 0-15 |
||
|
Channel rate |
802.11b: 1, 2, 5.5, 11 |
|
|
802.11a/g: 6, 9, 12, 18, 24, 36, 48, 54 |
||
|
802.11n: 6.5 to 300 (MCS0 to MCS15) |
||
|
802.11n high throughput support: 20/40 |
||
|
Channel quantity |
802.11a, 802.11n (compatible with 802.11a): 5 channels |
|
|
802.11b, 802.11g, 802.11n (compatible with 802.11b/g mode): 13 channels |
||
|
Manual and automatic channel adjustment |
Supported |
|
|
Automatic power adjustment |
Supported |
|
|
Manual power adjustment |
The AP supports manual power adjustment with an adjustment granularity of 1 dBm. The power scope is from 1 dBm to the value specified by national regulations. |
|
|
Timed turning on or off of RF |
RF can be turned on or off based on the specified time period. |
|
|
Turn off MIMO |
Supported. An RF interface can be selected for single output. |
|
|
WLAN function |
Maximum number of connected users |
256 (maximum number of connected users of a single RF: 128) |
|
Connected user quantity restriction |
Supported |
|
|
Virtual AP |
32 |
|
|
Chinese SSID |
Supported |
|
|
SSID hiding |
Supported |
|
|
Wireless relay/bridge |
Point-to-point and point-to-multipoint supported |
|
|
User-, traffic-, and frequency band-based intelligent load balancing |
Supported |
|
|
Bandwidth restriction |
STA-, SSID-, or AP-based rate limiting is supported. |
|
|
STA function |
Abnormal STA disconnection detection, STA aging detection, and STA statistic and status query are supported. |
|
|
Link integrity detection |
Supported |
|
|
Security authentication |
Authentication mode |
Pre-shared key authentication, portal authentication, 802.1x authentication, CA certificate authentication, WeChat authentication, SMS authentication, 2-dimensional code authentication, temporary visitor authentication, and authentication exemption are supported. |
|
Pre-shared key |
WPA-PSK, WPA2-PSK, WPA-PSK/WPA2-PSK hybrid authentication |
|
|
Portal authentication |
Intelligent terminal type identification is supported. A page matching the terminal size is pushed to terminals. The page logo and displayed information can be customized. In addition, the verification, authentication interval, and reconnection authentication time thresholds can be set. |
|
|
802.1x authentication |
802.1x one-key configuration and 802.1x perception-free authentication are supported. You only need to download the one-key automatic configuration tool at initial access and finish wireless network configuration quickly. This simplified network deployment significantly. |
|
|
CA certificate authentication |
High-security certificate authentication can be implemented by using the CA certificate issuance center embedded into the controller, without the need to constructing a certificate server. Authentication by using a certificate imported from an external certificate server is also supported. |
|
|
WeChat authentication |
After access the wireless network, a user can scan the 2-dimensional code of the shopping mall or enterprise and follow the public account to access the Internet. The one-key follow function can be easily deployed without any code development. In WeChat authentication, a user can access the network by clicking a text message network access link or clicking the menu bar to view advertisements, or access the network via WeChat authorization. |
|
|
SMS authentication |
SMS authentication takes effect forever. That is, a user can directly access the network without authentication after being authenticated via SMS at initial access. This reduces the SMS costs and improves user experience. |
|
|
2-dimensional code authentication |
After a visitor terminal accesses the wireless network, the terminal will automatically display a 2-dimensional page. The approver scans the 2-dimensional code of the visitor terminal via a cell phone and then the visitor can access the Internet. The visitor information is recorded in three dimensions: approver, remarks, and MAC address of the visitor terminal. This ensures user traceability and network security. |
|
|
Temporary visitor authentication |
A temporary user information management system is embedded. A temporary user can log in within the validity period and cannot after the validity period elapses. A secondary permission system for temporary account management is embedded and temporary accounts can be created and managed in this system. The 2-dimensional code of a temporary visitor can be printed and the temporary visitor can scan the 2-dimensional code to access the network. Temporary visitors can be grouped. |
|
|
Authentication exemption |
Only a portal advertisement page is displayed. A user needs to click the login button to access the network without entering any account password or performing other authentication. |
|
|
Data encryption |
Data encryption via TKIP and AES (CCMP) is supported. |
|
|
Blacklist and whitelist |
Static whitelist and blacklist are supported. |
|
|
User isolation |
SSID-based isolation, automatic VLAN grouping, and user isolation of specified VLANs are supported. |
|
|
WIPS |
Supported |
|
|
Illegitimate AP detection and workaround |
Supported |
|
|
ACL |
Account-, access location-, access terminal type- and SSID-based ACL policy assignment and management are supported. |
|
|
Radius protocol |
Supported |
|
|
Wireless optimization |
Application layer acceleration |
Acceleration can be performed for the application layer. The acceleration service application can help increase the transmission speed by 1.5 to 4 times. |
|
E-schoolbag scenario optimization |
The transmission speed of multicast packets is increased, improving the effects of the E-schoolbag scenario in an all-round way. |
|
|
Intelligent broadcast acceleration |
The transmission speed of broadcast packets is automatically increased based on the actual environment, thereby improving the transmission efficiency of broadcast packets. |
|
|
Terminal dragging prevention |
This function aims to prevent the decrease of the entire network speed caused by low-speed terminals based on the time fairness algorithm. |
|
|
Terminal viscosity prevention |
This function involves detecting STAs connected to APs and intelligently guiding the STAs to the optimal AP. |
|
|
Prohibited access of low-speed terminals |
The speed of access terminals is limited. Weak-signal terminals with a speed lower than the specified value are prohibited from accessing the network. This improves the entire network speed. |
|
|
High-density access scenario optimization |
The response to broadcast probe requests is controlled for the purpose of optimizing high-density access scenarios. |
|
|
ARP-unicast conversion |
ARP broadcast packets are converted into unicast packets. This reduces the number of broadcast packets, thereby improving the transmission speed. |
|
|
Prohibit DHCP requests destined for wireless terminals |
After this function is enabled, DHCP broadcast requests will be forwarded only to the wired network, instead of other wireless network. This improves the network throughput and performance of the wireless network. |
|
|
Hotspot analysis |
AP-based access user quantity statistics |
The number of connected users and change trends of each AP in the recent one day, one week, and one month can be measured. |
|
AP-based network access traffic statistics |
The network access traffic and change trends of each AP in the recent one day, one week, and one month can be measured. |
|
|
AP-based signal quality analysis |
Statistic analysis for the signal usage, noise, retransmit rate, BER, and BER change trends of each AP is supported. |
|
|
AP access mode |
AC discovery mechanism |
L2 broadcast automatic discovery |
|
L3 discovery based on configured static IP addresses |
||
|
DHCP Option43 discovery |
||
|
DNS domain name discovery |
||
|
Cross-WAN and cross-NAT remote AP deployment |
Supported |
|
|
webAgent |
Controller IP addresses can be dynamically discovered by using the webAgent technology. This avoids AP disconnection caused by unfixed controller IP addresses. |
|
|
Tunnel encryption |
Supported |
|
|
Wireless relay/bridge |
Relay mode |
Point-to-point and point-to-multipoint supported |
|
Relay frequency band |
2.4/5.8 GHz |
|
|
Disable wireless network on relay frequency band |
Supported |
|
|
Wireless backhaul service |
Supported |
|
Bu ürüne ait özellikler veritabanımızda bulunmamamktadır.
Bu ürüne alternatif bir ürün bulunmamaktadır.